John Package Description. John the Ripper is designed to be both feature-rich and fast. It combines several cracking modes in one program and is fully configurable for your particular needs (you can even define a custom cracking mode using the built-in compiler supporting a subset of C). Also, John is available for several different platforms. Break Windows 10 password hashes with Kali Linux and John the Ripper. Cracking the SAM file in Windows 10 is easy with Kali Linux. Use a Live Kali Linux DVD and mount the Windows 10 partition. Firstly, get the SAM and SYSTEM files from the C: Windows System32 config folder. Copy these to your desktop directory. Then dump the password hashes.
John The Ripper is an open source and very efficient password cracker by Open-Wall. It was originally built for Unix but is now available for fifteen different platforms including Windows, DOS, BeOS, OpenVMS and Unix like operating systems. It is an Open Source tool and is free, though a premium version also exists. Initially, its primary purpose was to detect weak password configurations in Unix based Operating systems. Today it supports cracking of hundreds of hashes and ciphers.Installation
John The Ripper can be installed in many ways. A few common ones are we can install it by using apt-get or snap. Open up the terminal and run the following commands.
This will initiate an installation process. Once it finishes type ‘john’ in the terminal.
John the Ripper 1.9.0-jumbo-1 OMP [linux-gnu 64-bit 64 AVX2 AC]
Copyright (c)1996-2019 by Solar Designer and others
Homepage: http://www.openwall.com/john/
This means John the Ripper v1.9.0 is now installed on your device. We can see the homepage URL sending us to Open-wall’s website. And Usage given below indicates how to use the utility.
It can also be downloaded and installed via snap. You need to install snap if you do not already have it.
[email protected]:~$ sudo apt install snapd
And then install JohnTheRipper via snap.
Cracking Passwords with JohnTheRipper
So, JohnTheRipper is installed on your computer. Now to the interesting part, how to crack passwords with it. Type ‘john’ in the terminal. The Terminal will show you the following result:
How To Install John The Ripper Windows 7 64-bit
John the Ripper 1.9.0-jumbo-1 OMP [linux-gnu 64-bit 64 AVX2 AC]
Copyright (c)1996-2019 by Solar Designer and others
Homepage: http://www.openwall.com/john/
Below the Homepage, USAGE is given as:
Usage: john [OPTIONS][PASSWORD-FILES]
By looking at its usage, We can make out that you just need to supply it your password file(s) and the desired option(s). Different OPTIONS are listed below the usage providing us different choices as to how the attack can be carried out.
Some of the different options available are:
–single
- Default mode using default or named rules.
–wordlist
- wordlist mode, read wordlist dictionary from a FILE or standard input
–encoding
- input encoding (eg. UTF-8, ISO-8859-1).
–rules
- enable word mangling rules, using default or named rules.
–incremental
- ”incremental” mode
–external
- external mode or word filter
–restore = NAME
- restore an interrupted session [called NAME]
–session = NAME
- name a new session NAME
–status = NAME
- print status of a session [called NAME]
–show
- show cracked passwords.
–test
- run tests and benchmarks.
–salts
- load salts.
–fork = N
- Create N processes for cracking.
–pot = NAME
- pot file to use
–list = WHAT
- lists WHAT capabilities. –list=help shows more on this option.
–format = NAME
- Provide John with the hash type. e.g, –format=raw-MD5, –format=SHA512
Different modes in JohnTheRipper
By default John tries “single” then “wordlist” and finally “incremental”. Modes can be understood as a method John uses to crack passwords. You may have heard of different kinds of attacks like Dictionary attack, Bruteforce attack etc. That precisely, are what we call John’s modes. Wordlists containing possible passwords are essential for a dictionary attack. Apart from the modes listed above John also supports another mode called external mode. You can choose to select a dictionary file or you can do brute-force with John The Ripper by trying all possible permutations in the passwords. The default config starts with single crack mode, mostly because it’s faster and even faster if you use multiple password files at a time. The most powerful mode available is the incremental mode. It will try different combinations while cracking. External mode, as the name implies, will use custom functions that you write yourself, while wordlist mode takes a word list specified as an argument to the option and tries a simple dictionary attack on passwords.
How To Install John The Ripper Windows 10
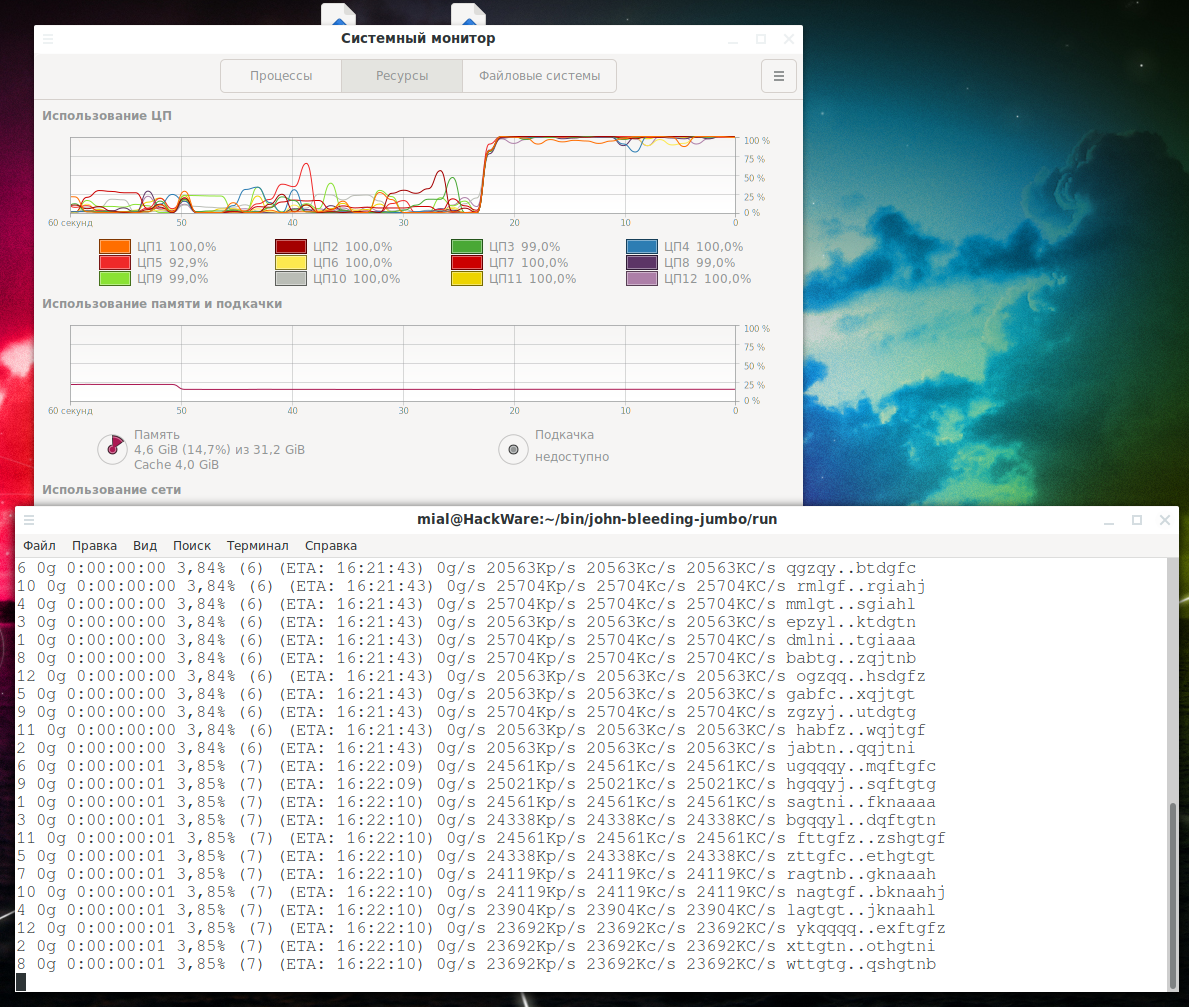
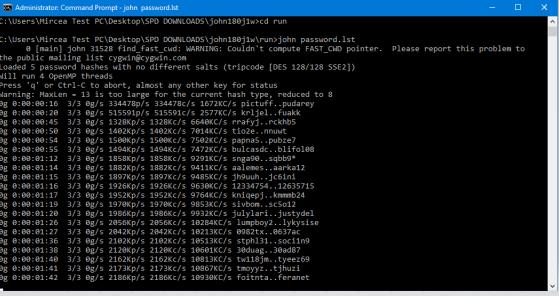
John will now start checking against thousands of passwords. Password cracking is CPU-intensive and a very long process, so the time it takes will depend on your system and the strength of the password. It can take days. If the password is not cracked for days with a powerful CPU, it is a very good password. If it is really crucia; to crack the password then leave the system until John cracks it.. As mentioned earlier, this can take many days.
As it cracks, you can check status by pressing any key. To Quit an attack session simply press ‘q’ or Ctrl + C.
Once it finds the password, it will be displayed on the terminal. All the cracked passwords are saved in a file called ~/.john/john.pot.
It displays passwords in $[HASH]:<pass> format.
$dynamic_0$827ccb0eea8a706c4c34a16891f84e7b:12345

Let’s crack a password. For instance, we have a MD5 password hash that we need to crack.
We will put this into a file, say password.hash and save it in user:<hash> format.
You can type any username, it is not necessary to have some specified ones.
Now we crack it!
It starts cracking the password.
We see that john loads hash from the file and starts with the ‘single’ mode. As it progresses, it goes onto the wordlist before moving onto incremental. When it cracks the password, it stops the session and shows the results.
Password can be seen later also by:
admin:emerald
1 password hash cracked, 0 left
Also by ~/.john/john.pot :
[email protected]:~$ cat ~/.john/john.pot
$dynamic_0$bd9059497b4af2bb913a8522747af2de:emerald
$dynamic_0$827ccb0eea8a706c4c34a16891f84e7b:12345
So, the password is emerald.
The internet is full of modern password cracking tools and Utilities. JohnTheRipper may have many alternatives, but it is one of the best ones available. Happy Cracking!
John the Ripper is free and Open Source software,distributed primarily in source code form.If you would rather use a commercial product, please considerJohn the Ripper Pro,which is distributed primarily in the form of 'native' packagesfor the target operating systems and in general is meant to be easier toinstall and use while delivering optimal performance.
Proceed to John the Ripper Pro homepage for your OS:
Download the latest John the Ripper jumbo release(release notes) or development snapshot:
Run John the Ripper jumbo in the cloud (AWS):
Download the latest John the Ripper core release(release notes):
|
These and older versions of John the Ripper, patches, unofficial builds, and many other related files are alsoavailable from the Openwall file archive.
You can browse the documentation for John the Ripper core online, including asummary of changes between core versions.Also relevant is ourpresentation on the history of password security.
There's a collection of wordlists for use with John the Ripper.It includes lists of common passwords, wordlists for 20+ human languages, and files with the common passwords andunique words for all the languages combined, also with mangling rules applied and any duplicates purged.
yescrypt and crypt_blowfishare implementations of yescrypt, scrypt, and bcrypt - some of the strong password hashes also found in John the Ripper -released separately for defensive use in your software or on your servers.
How To Install John The Ripper Windows 7 Free
passwdqc is a proactive password/passphrase strength checking and policy enforcement toolset,which can prevent your users from choosing passwords that would be easily cracked with programs like John the Ripper.
We can help you integrate modern password hashing withyescrypt or crypt_blowfish,and/or proactive password strength checking withpasswdqc,into your OS installs, software, or online services.Please check out our services.
There's a mailing list where you can share your experience with John the Ripper and ask questions.Please be sure to specify an informative message subject wheneveryou post to the list(that is, something better than 'question' or 'problem').To subscribe, enter your e-mail address below or send an empty message to<john-users-subscribe at lists.openwall.com>.You will be required to confirm your subscription by 'replying'to the automated confirmation request that will be sent to you.You will be able tounsubscribeat any time and we will not use your e-mailaddress for any other purpose or share it with a third party.However, if you post to the list, other subscribers and thoseviewing the archives may see your address(es) as specified on your message.The list archive is availablelocally and viaMARC.Additionally, there's alist of selected most useful and currently relevant postings on thecommunity wiki.
Contributed resources for John the Ripper:
|
How To Install John The Ripper In Windows 10
Local copies of these and many other related packages are alsoavailable from the Openwall file archive.John the Ripper is part ofOwl,Debian GNU/Linux, Fedora Linux, Gentoo Linux, Mandriva Linux, SUSE Linux,and a number of other Linux distributions.It is in the ports/packages collections of FreeBSD, NetBSD, and OpenBSD.
John the Ripper is a registered project withOpen Huband it is listed atSecTools.